How Retailers Can Avoid Being a Target for Security Breaches
Everyone’s too familiar with all the data security breaches occurring at some of the nation’s largest retailers. The impact has gone far beyond the companies themselves and their proprietary data. The latest hacks have directly hit consumers as personally identifiable information (PII) as well as credit and debit card data have been stolen and sold on the black market.
One of the differences in some of these recent system break-ins has been that the hackers haven’t hacked into the retailers’ systems directly. Directly accessing a corporation’s networks through firewalls and secure barriers can in fact prove quite difficult. But like the cliche movie scene where someone rides into (or out of) a secure facility by sneaking under a truck and holding onto it as it drives through security, piggybacking in via ‘official’ channels is one of these hackers’ preferred modus operandi. Like any attack, going through the weakest link, which in many cases is an outside party with legitimate system access, can prove successful.
What Are Companies Doing Wrong?
How are such breaches occurring, and more importantly, what strategies should you follow to prevent them? Let’s see some of the inherent flaws certain companies’ systems have and how the concept of Cloud-based Isolation can help.
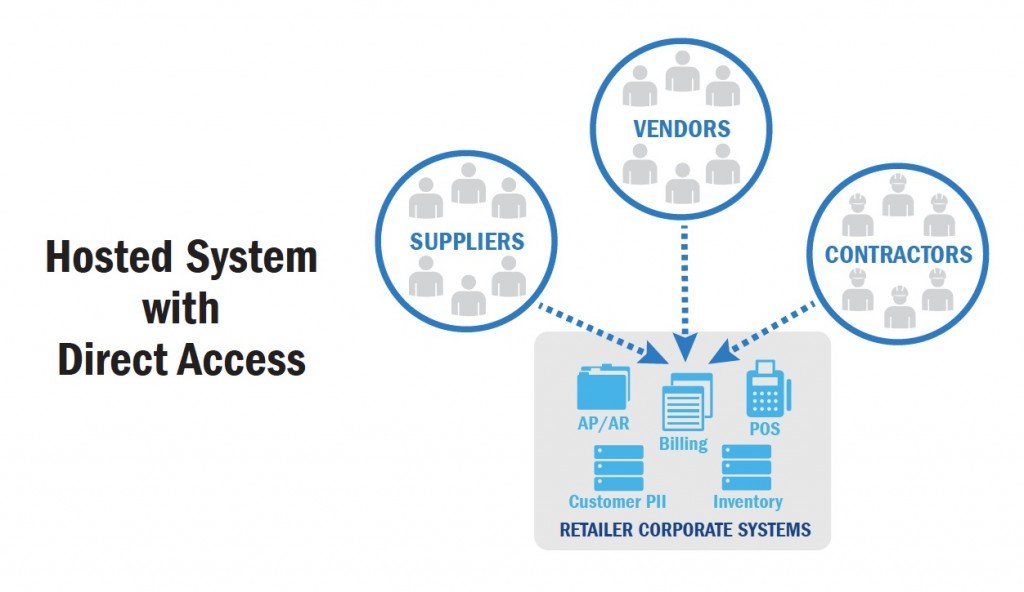
Every company has firewalls, network detection systems and all sorts of digital countermeasures in place to prevent unwanted access. The problem is with the ‘wanted’ access. Today’s business environment requires collaboration between a company and a multitude of vendors, suppliers, customers, contractors and consultants among others.
Unfortunately, companies often provide direct access through their secure barriers to these partners to access internal systems like billing applications (e.g. to submit invoices directly). Basically, what they’ve done is build a wall and then allowed their trusted partners a way through it.
The Weakest Link
That’s fine as these third parties require passwords and other authorizations, right? Well, the problem is that’s not a highly secure approach. In fact, it’s proven to be the ‘weak link’ in the system. There have been cases where outside contractors have had credentials stolen (e.g. via online phishing scams), allowing hackers direct access into a retailer’s hosted system.
But the problem doesn’t stop at the billing system. Once inside a hosted system for vendors on the retailer’s network, the hackers then use their nefarious tricks of the trade to gain unfettered access from that first vendor system, over its internal corporate network, to all of a retailer’s systems, across its entire geographic footprint.
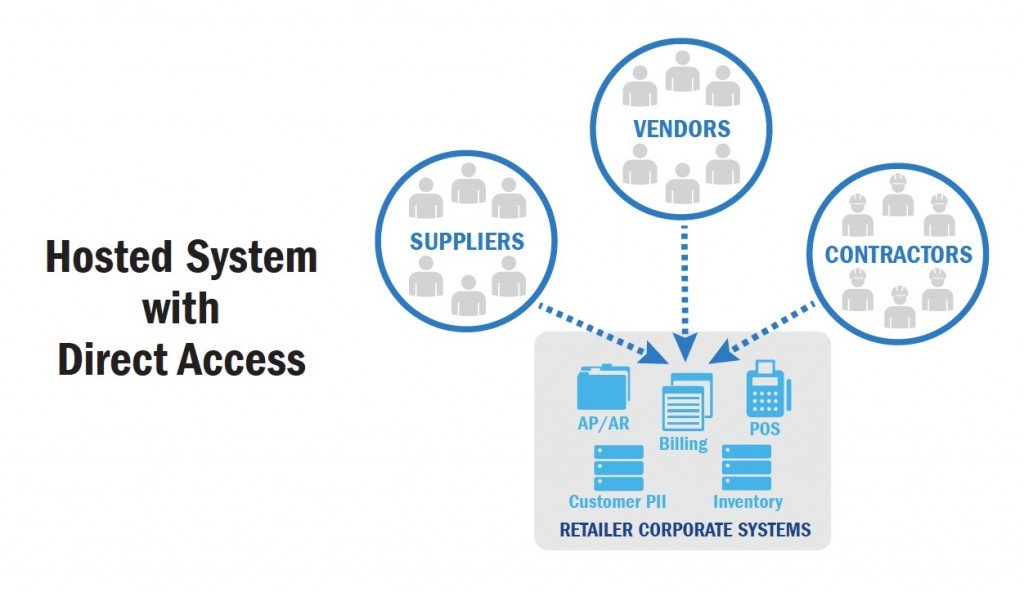
In such cases, they’ve hacked into and accessed customer data, and even infected in-store POS systems (e.g., card readers) to capture credit/debit card data during each transaction. Thus, allowing direct access to internally hosted systems for a contractor to submit an invoice electronically, can quickly lead to a customer’s financial data being stolen while making a purchase at a remote location. Then multiply that by tens of millions!
Cloud-based Isolation
Luckily, this doesn’t have to happen. Through the deployment of cloud-based technologies, third parties and external (to the company) users can still exchange key data but not serve as conduits to illegal digital access.
By utilizing cloud-based deployment for such collaborative systems, contractors and vendors can still access key operating data, submit invoices and proposals, and perform what other online tasks they need to. But only the cloud-based system has access into the retailer’s system, through an encrypted and secure single point of communication. This way, contractors and vendors never directly access a retailer’s system, and any compromised external accounts can’t gain entry.
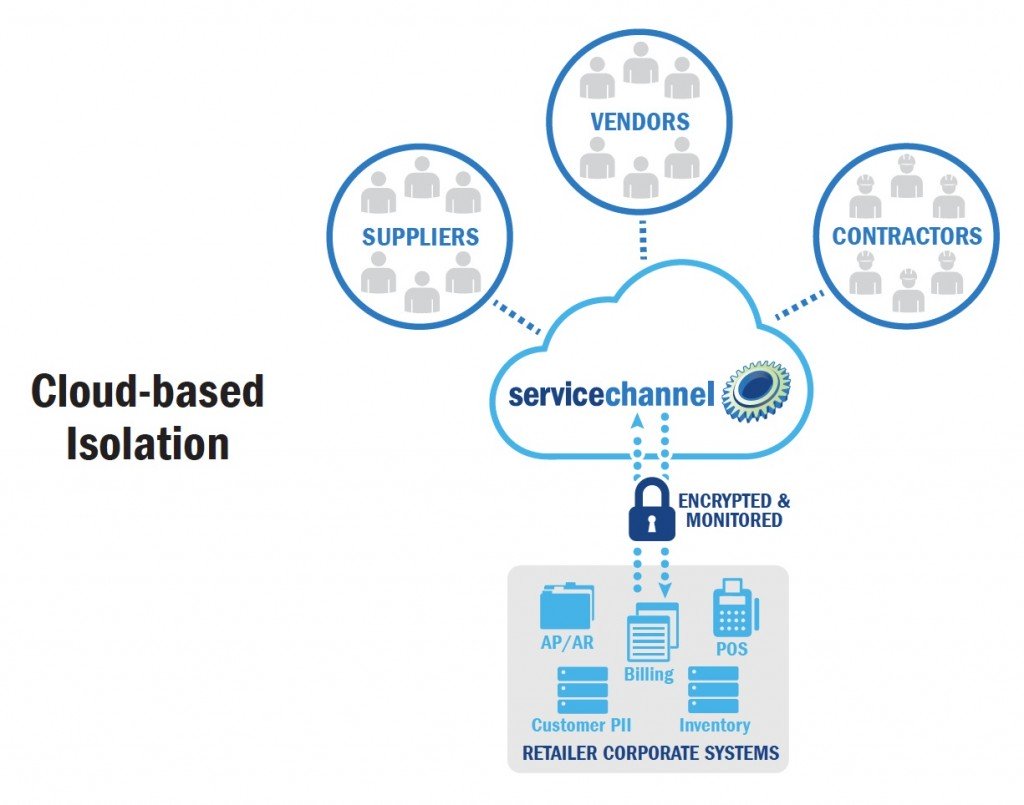
At ServiceChannel, we call this approach Cloud-based Isolation, and its one of the principal reasons why the leading retailers trust us to be a key part of their facilities infrastructure. This way, communication with our clients’ internal servers (e.g. data feeds for locations, invoices and payments) is tightly controlled, secured, encrypted and monitored.
Security is a constant battle as the guys in the black hats continually look for vulnerabilities. But by ensuring your facilities management system is based on Cloud-based Isolation, you can be confident that a principal avenue of attack has been closed.
Serge Lubensky is founder and Chief Technology Officer at ServiceChannel, the leading facilities services management platform. Serge was born and raised behind the Iron Curtain. After graduating first in class with a master’s degree in Computer Science but no prospects of finding freedom and happiness, he travelled from Minsk to New York to become a Principal Architect of Service Contractor Systems, a highly successful business software package for service contractors. At ServiceChannel, Serge combines his log2(33,554,432) years of experience in service contracting and facilities maintenance industries with software development expertise to lead product management and engineering teams.